Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
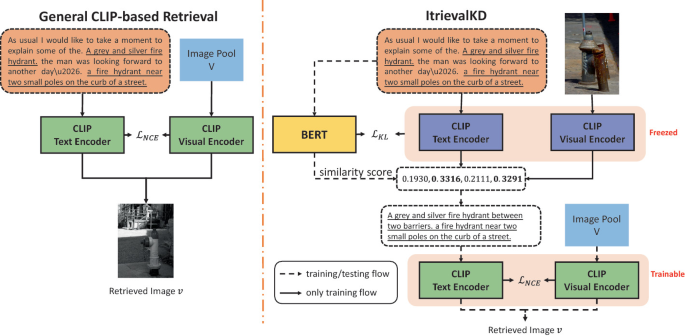
ItrievalKD: An Iterative Retrieval Framework Assisted with Knowledge Distillation for Noisy Text-to-Image Retrieval

PDF) A Study on the X-bar and S Control Charts with Unequal Sample Sizes
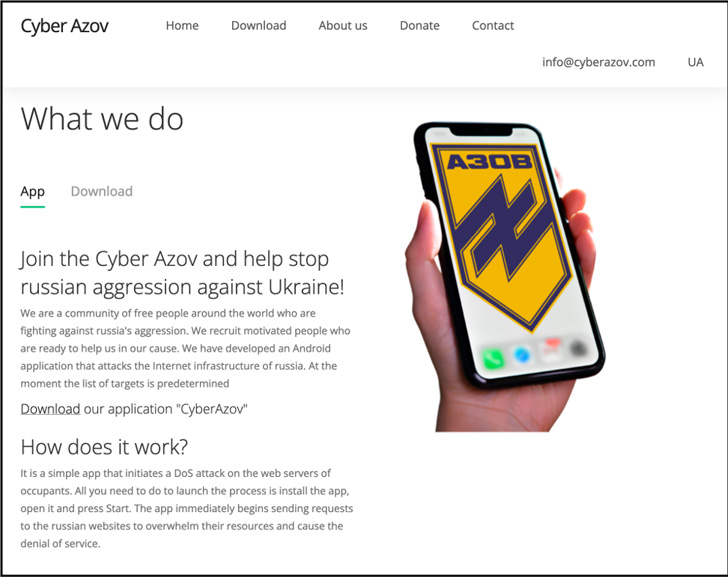
Russian Hackers Tricked Ukrainians with Fake DoS Android Ap - vulnerability database
Hackers Using Microsoft MSHTML Flaw to Spy on Targeted PCs w - vulnerability database
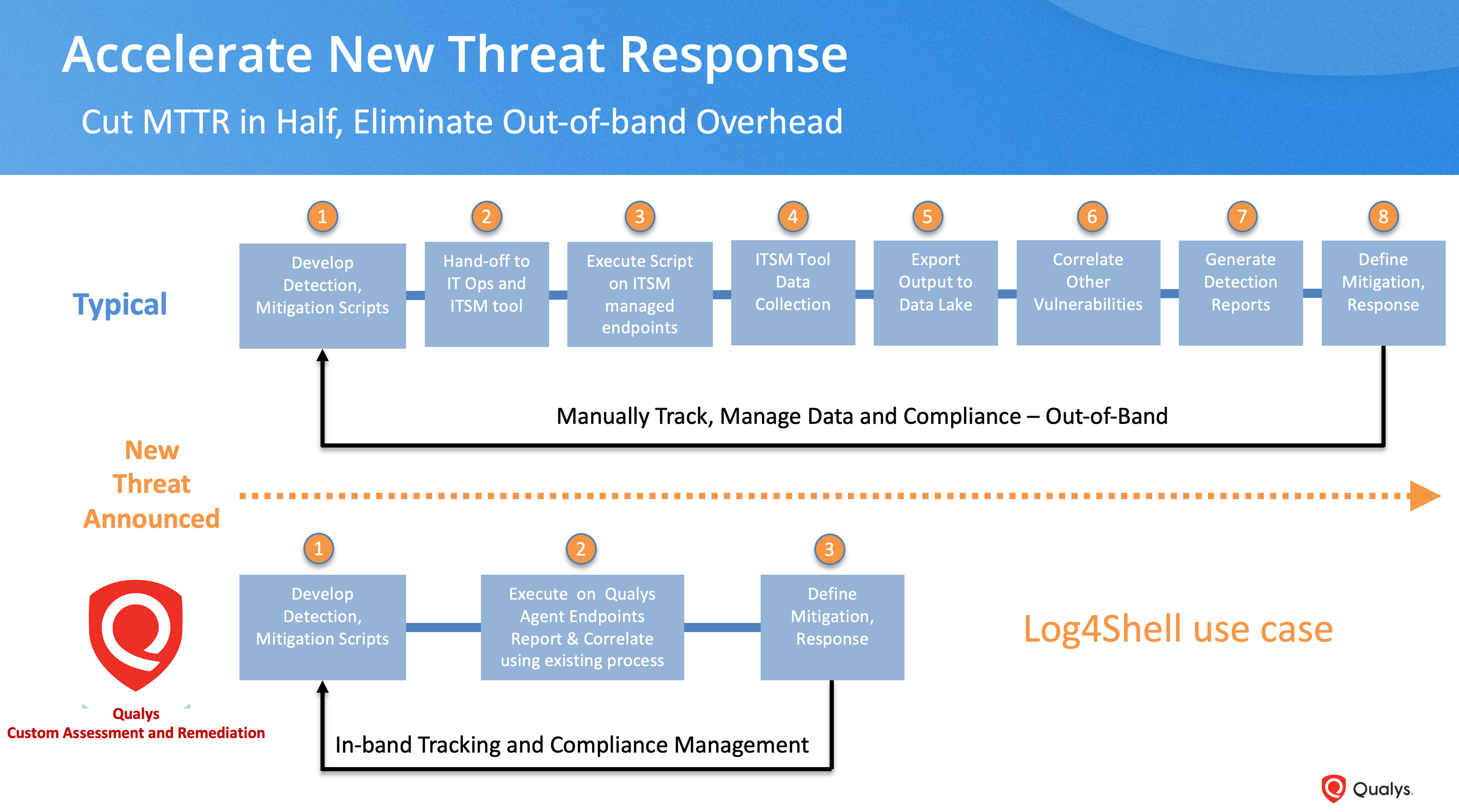
What's Next After Log4Shell? - vulnerability database
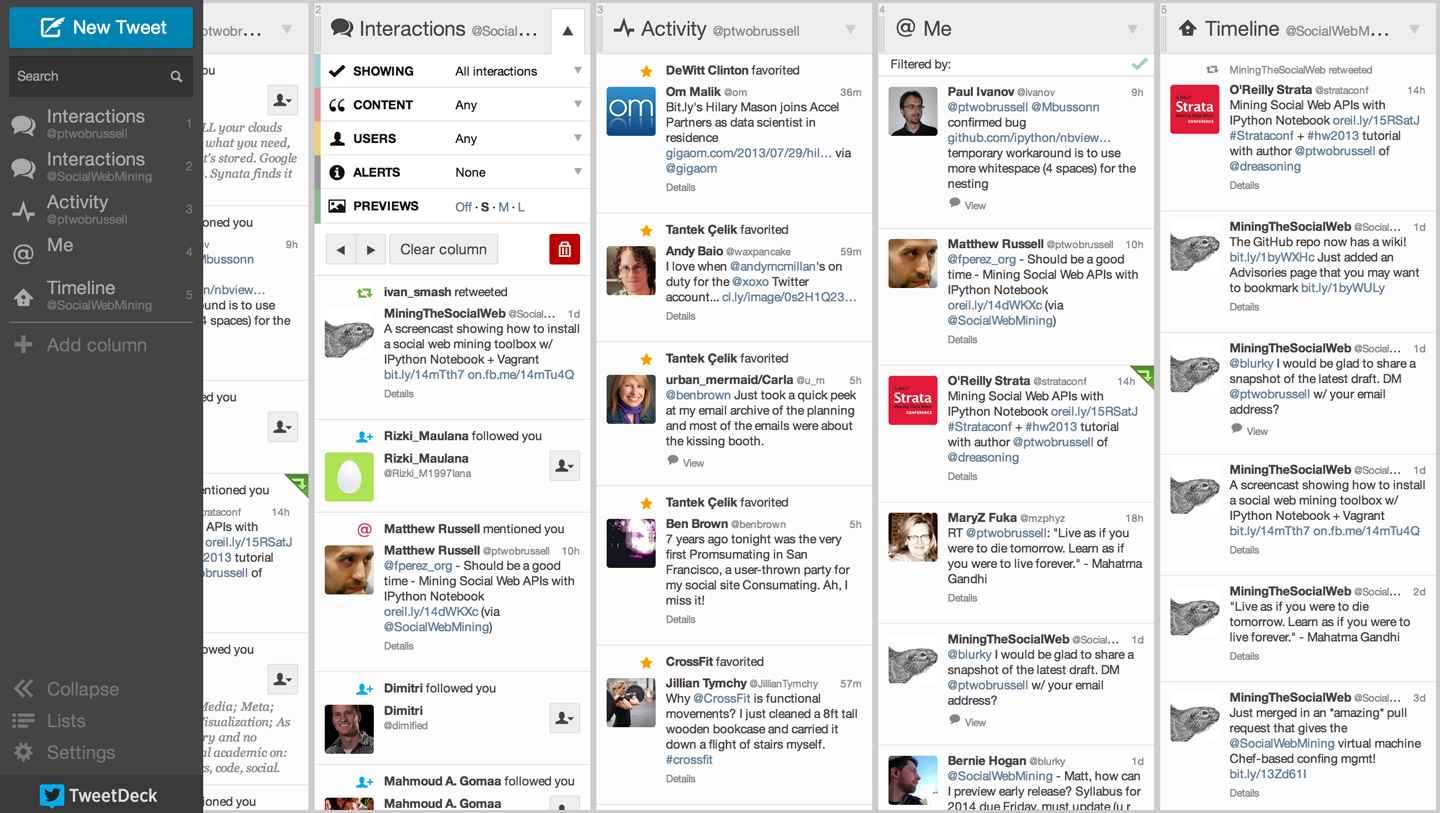
1. Mining Twitter: Exploring Trending Topics, Discovering What People Are Talking About, and More - Mining the Social Web, 3rd Edition [Book]
The role of endothelial MERTK during the inflam…

Iterable - Resources about Growth Marketing and User Engagement
IBM Tivoli Storage Manager: Building a Secure Environment - Urz
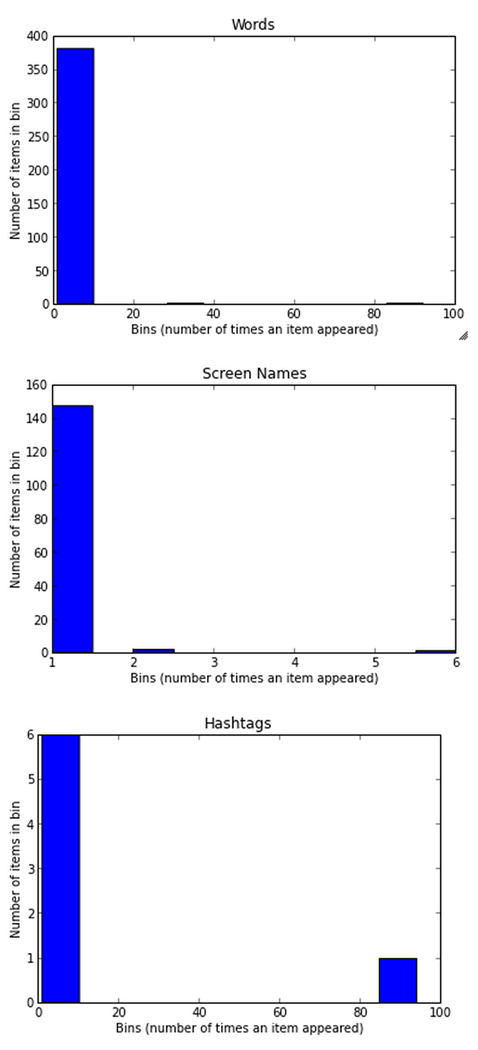
1. Mining Twitter: Exploring Trending Topics, Discovering What People Are Talking About, and More - Mining the Social Web, 3rd Edition [Book]
Twitter-Sentiment-Analysis/ikeatweet.txt at master · barryntsiba/Twitter-Sentiment-Analysis · GitHub
The domesticated transposase ALP2 mediates form…

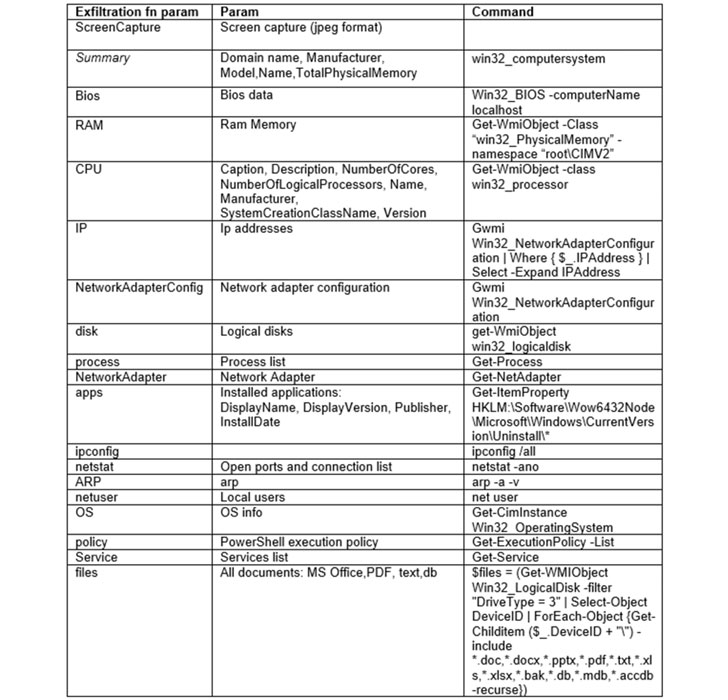
Exploitation of the CVE-2021-40444 vulnerability in MSHTML - vulnerability database

··· 게시글 프린트 화면 보기 ···
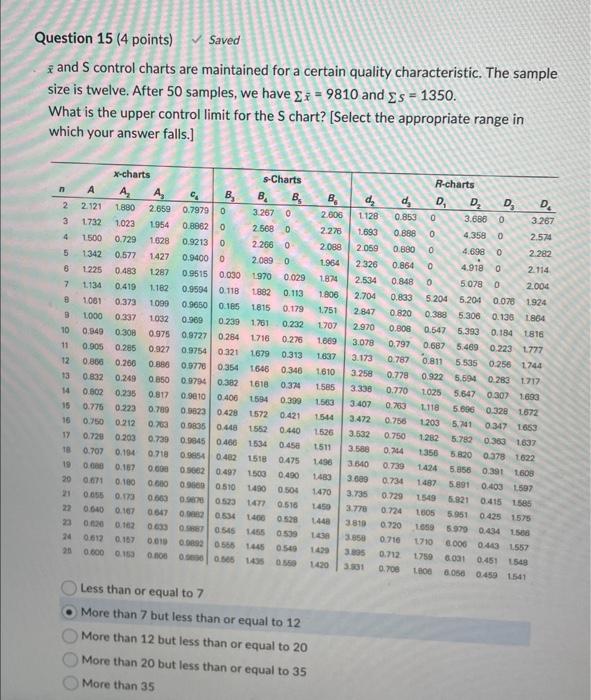
Solved xˉ and S control charts are maintained for a certain
Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
- Best Price $ 203.00. Good quality and value when compared to dichvuketoan.vn similar items.
- Seller - 313+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Louis Vuitton Sarah Wallet
Buy It Now 13d 14h -

Men's Rolling Luggage, Suitcases, Duffles, Carryons
Buy It Now 2d 23h -

Louis Vuitton Pink Monogram Empreinte Pochette Metis QJB0UEEHPB006
Buy It Now 20d 16h -

Pin by Ashley on bags in 2023 Louis vuitton duffle bag, Bags, Louis vuitton speedy bag
Buy It Now 22d 21h -
LOUIS VUITTON Men's Black White Damier Graphite Low Top Sneakers
Buy It Now 25d 5h -

Louis Vuitton Damier Ebene Evora MM (SHG-35399) – LuxeDH
Buy It Now 5d 16h -

Louis Vuitton (designer) - Wikipedia
Buy It Now 13d 9h -

Louis Vuitton Lumineuse PM Monogram Empreinte Bag Plum
Buy It Now 10d 11h -

Louis Vuitton Tactical Trousers in Gray for Men
Buy It Now 10d 9h -

Who Died in 'The White Lotus' Season 2 Finale? Ending Explained, Spoilers – StyleCaster
Buy It Now 24d 21h -

Louis Vuitton Delights Fans with the New LV² Collection
Buy It Now 17d 8h -

Everything to Know About Louis Vuitton's Speedy Bag – WWD
Buy It Now 11d 23h -

Louis+Vuitton+Chelsea+Shoulder+Bag+Brown+Canvas for sale online
Buy It Now 20d 13h -
✨DIOR✨ Diaper bag Brand new Selling $4100 Comes with full set Not available in Aus Sold out
Buy It Now 23d 18h -

How Emerging Designer Peter Do Is Creating His Own Rules
Buy It Now 4d 19h -

Apartment Louis Vuitton Suite, Toronto, Canada
Buy It Now 11d 16h -

Gucci Shoulder Bag
Buy It Now 11d 16h -

Ari and Cama Crop Windbreaker — MARICAMA
Buy It Now 21d 14h -

Buy Cheap Louis Vuitton Shoes for Women's Louis Vuitton Sneakers
Buy It Now 25d 23h -

Louis Vuitton Shoe Stencil
Buy It Now 27d 7h -

4694 by Coaster - Paula Rectangular Cedar Chest Warm Brown
Buy It Now 11d 9h -

Shop Louis Vuitton ZIPPY WALLET Monogram Unisex Calfskin Street
Buy It Now 21d 6h -

Louis Vuitton Speedy Bandoulière 30 Damier Ebene Canvas - A World Of Goods For You, LLC
Buy It Now 9d 21h -

Louis Vuitton Métis Hobo Monogram - SOLD
Buy It Now 26d 13h

