Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…

Calaméo - Creswel L Qualitative Inquiry And Research
rapidminer-studio/src/main/resources/com/rapidminer/resources/i18n/GUI.properties at master · rapidminer/rapidminer-studio · GitHub
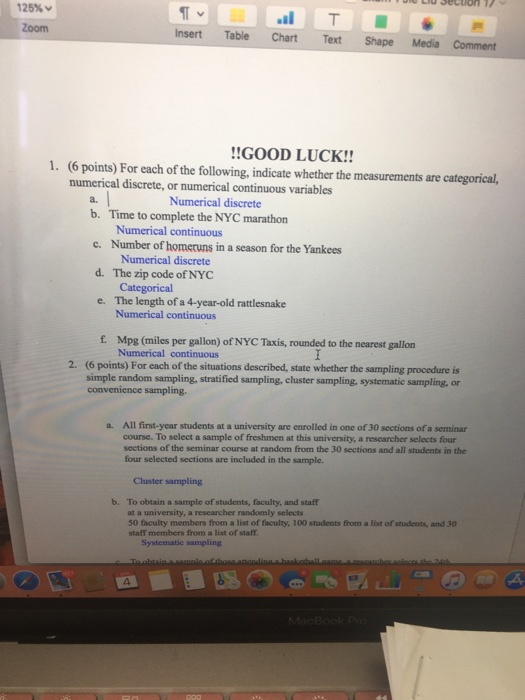
Solved U LIU Secuon 1 125% Zoom T il T Chart Text Insert
Hackers Using Microsoft MSHTML Flaw to Spy on Targeted PCs w - vulnerability database
The role of endothelial MERTK during the inflam…
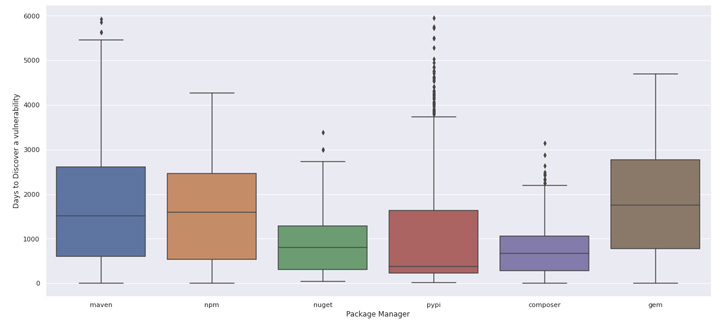
Last Years Open Source - Tomorrow's Vulnerabilities - vulnerability database
Watson
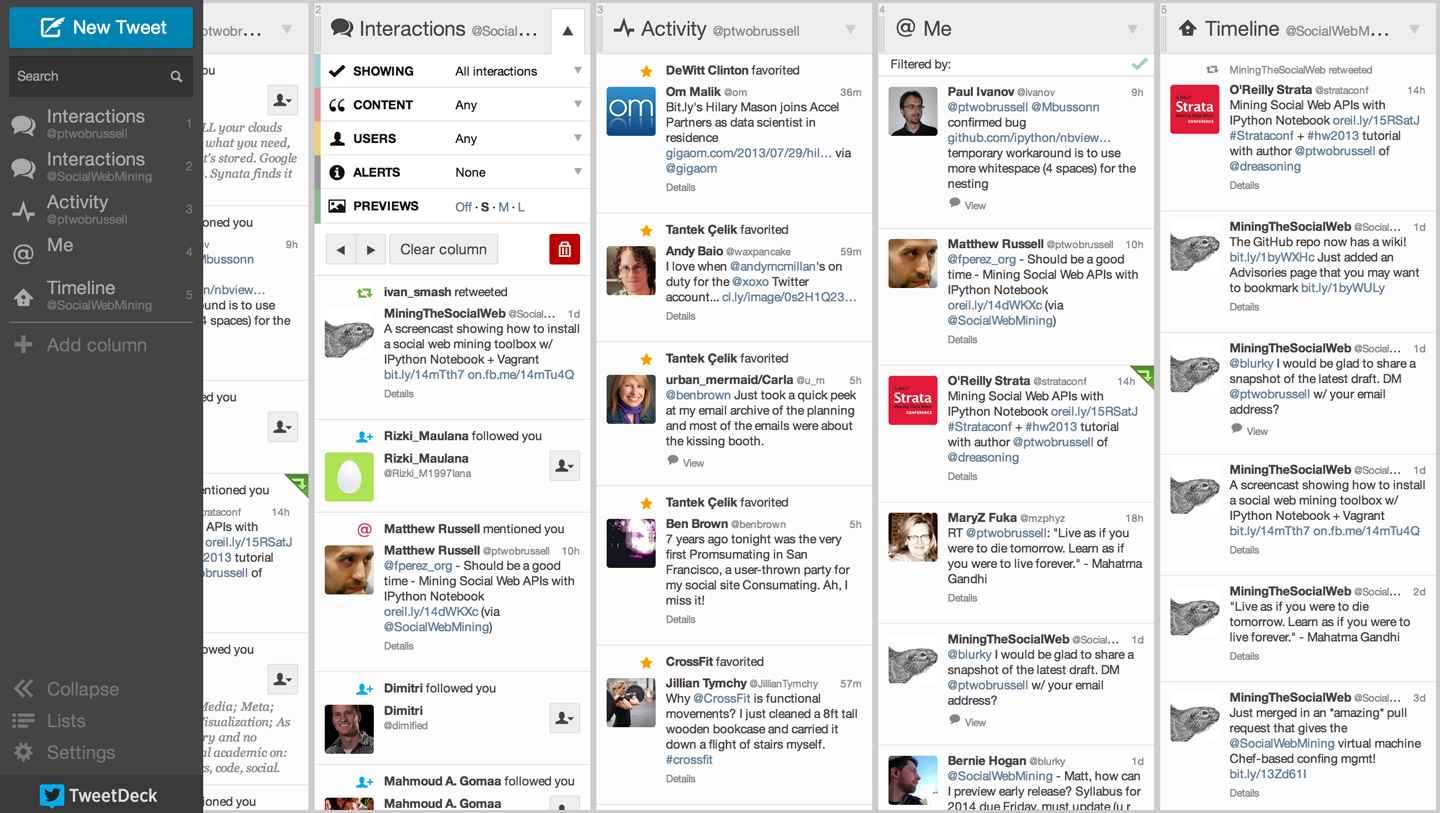
1. Mining Twitter: Exploring Trending Topics, Discovering What People Are Talking About, and More - Mining the Social Web, 3rd Edition [Book]
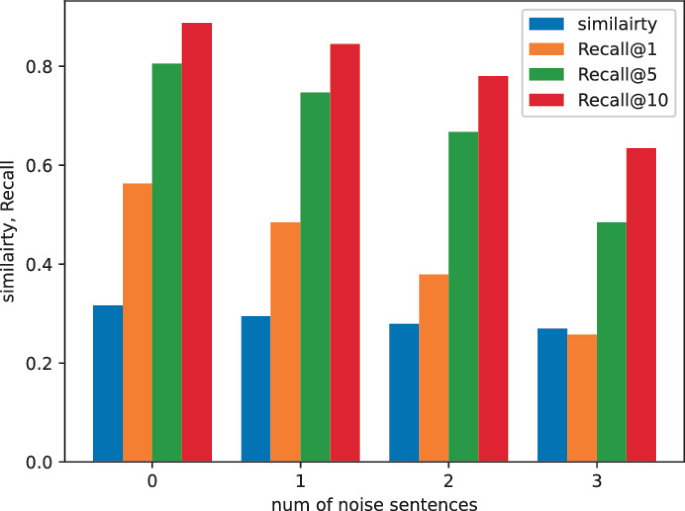
ItrievalKD: An Iterative Retrieval Framework Assisted with Knowledge Distillation for Noisy Text-to-Image Retrieval

What's happening in the world of crimeware: Emotet, DarkGate - vulnerability database

Drupal 8.3.9 8.4.6 8.5.1 - Drupalgeddon2 Remote Code Executio - exploit database
pydata2014-berlin/strata_abstracts.json at master · furukama/pydata2014-berlin · GitHub
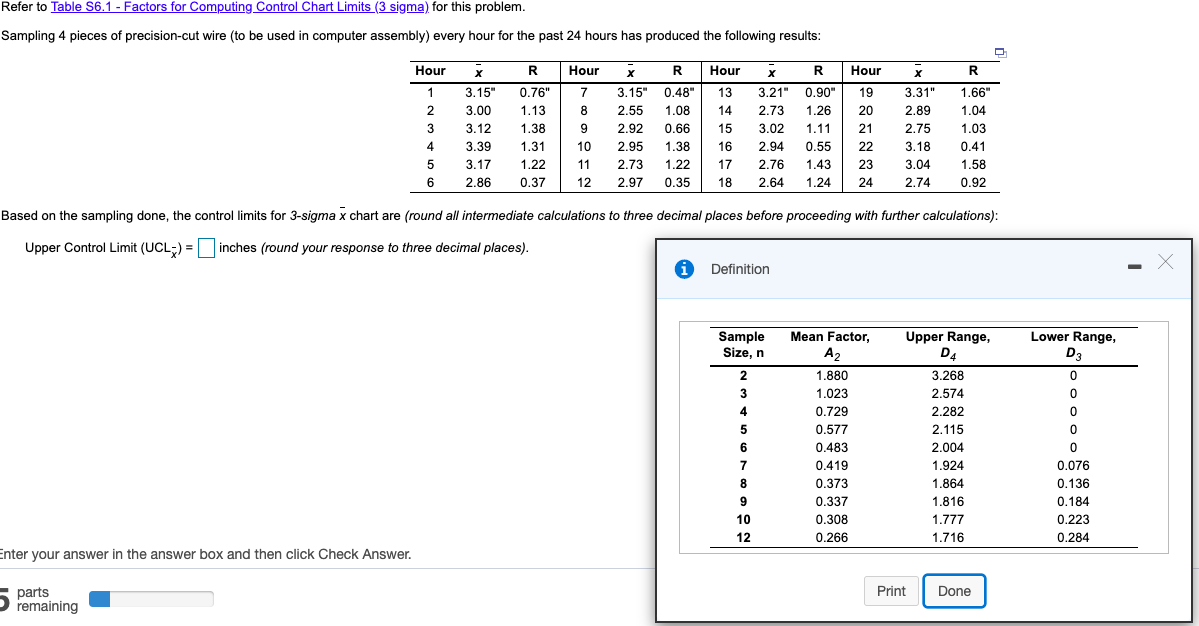
Solved Control limits for 3-sigma x chart are: -Upper
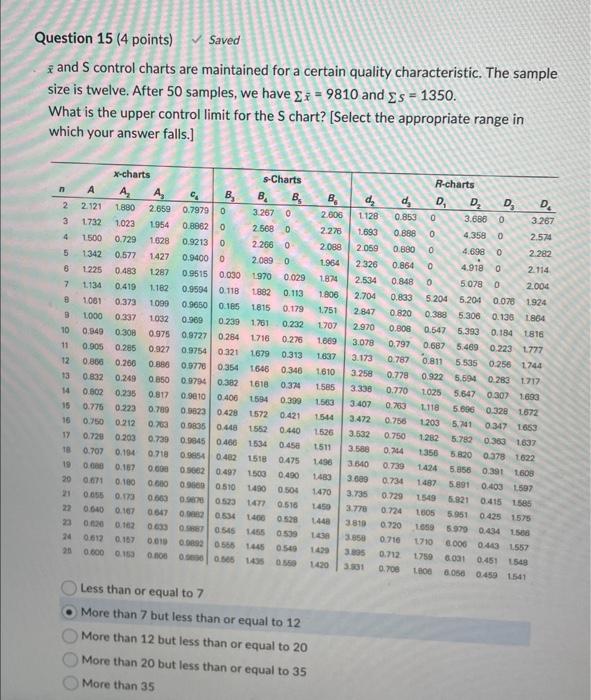
Solved xˉ and S control charts are maintained for a certain
The domesticated transposase ALP2 mediates form…
Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
- Best Price $ 248.99. Good quality and value when compared to dichvuketoan.vn similar items.
- Seller - 562+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Louis Vuitton Fleece Shearling Monogram Teddy Bumbag Fanny Pack Waist Pouch 930lv28
Buy It Now 23d 6h -

What's In My Diaper Bag
Buy It Now 16d 16h -

LV Montorgueil GM M95566 Brown Monogram Canvas with Leather and Gold Hardware #GLREL-3 – Luxuy Vintage
Buy It Now 14d 10h -

Changes Luxury Consignment, Scranton
Buy It Now 2d 10h -

Louis Vuitton LV x YK Trio Messenger Eclipse Monogram Eclipse
Buy It Now 4d 16h -

Louis Vuitton Printemps Bag
Buy It Now 6d 19h -

LOUIS VUITTON Damier Paillettes Speedy 30 Blue 729327
Buy It Now 11d 21h -

MC Stan Net Worth: His Luxury Cars, Career Earnings, Assets And More
Buy It Now 19d 5h -

CEO Frédéric Arnault Archives - Luxury Watch Trends 2018
Buy It Now 19d 6h -

Louis Vuitton Women's Danube Monogram Canvas M45266 Brown With Strap - Shop Linda's Stuff
Buy It Now 4d 18h -

Arjun Rampal on Ranveer Singh taking up 'Don 3': He will give - India Today
Buy It Now 11d 20h -

Supreme True Religion Denim Trucker Jacket
Buy It Now 28d 11h -

Nouvel Heritage: Fine Jewelry
Buy It Now 16d 12h -

ZANZEA Long Cape Coat Women Hooded Cloak Overcoat Poncho Coats
Buy It Now 12d 14h -

PHOTOS: Shai Gilgeous-Alexander at the 2023 Met Gala
Buy It Now 14d 22h -

Saint Laurent Sac de Jour Nano in Grained Leather
Buy It Now 21d 9h -

CALVIN KLEIN Pencil Case BACK TO SCHOOL Black
Buy It Now 7d 22h -

Louis Vuitton EPI Neverfull MM
Buy It Now 20d 10h -

How to Print, Cut & Fold Your Own DIY Hermès Handbag « Fashion
Buy It Now 9d 5h -

Small Robinson Perforated Satchel: Women's Designer Satchels
Buy It Now 18d 14h -

Calzado para hombre Nike Air Force 1 07 LV8 1
Buy It Now 3d 5h -

2pcs Silicone Leaf Fondant Mold 3D Leaves Shape Moulds Cake Baking Mould DIY Craft Decorating Tools for Polymer Clay Sugar Soap by RuiChy : Arts, Crafts & Sewing
Buy It Now 21d 18h -

Louis Vuitton Seamless Pattern Shirt - Vintagenclassic Tee
Buy It Now 22d 19h -

Louis Vuitton Iphone Case(include box), Mobile Phones & Gadgets
Buy It Now 14d 11h
