Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
$ 13.00 Buy It Nowor Best Offer, FREE Shipping, 30-Day Returns
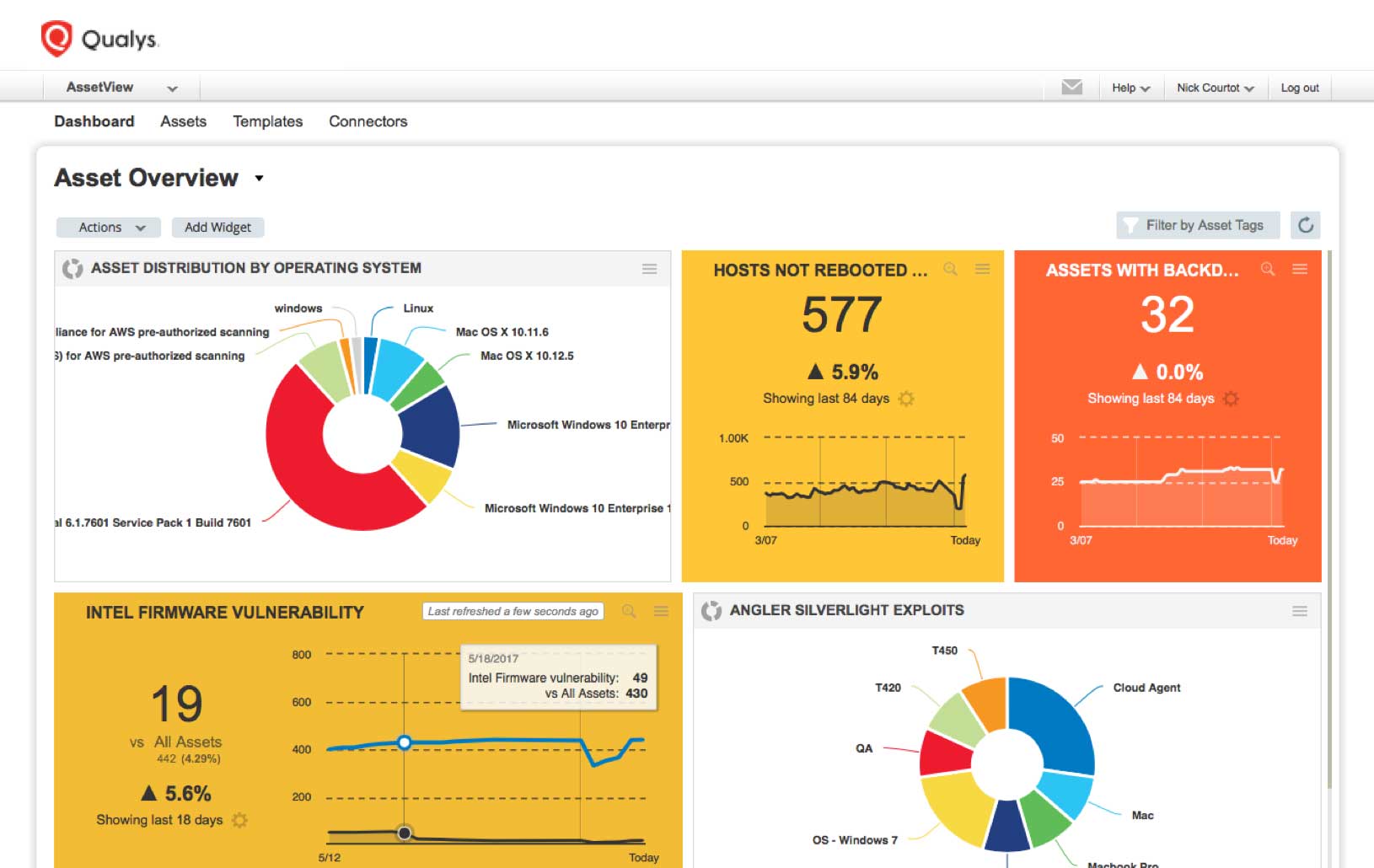
How To Prioritize Vulnerabilities in a Modern IT Environment
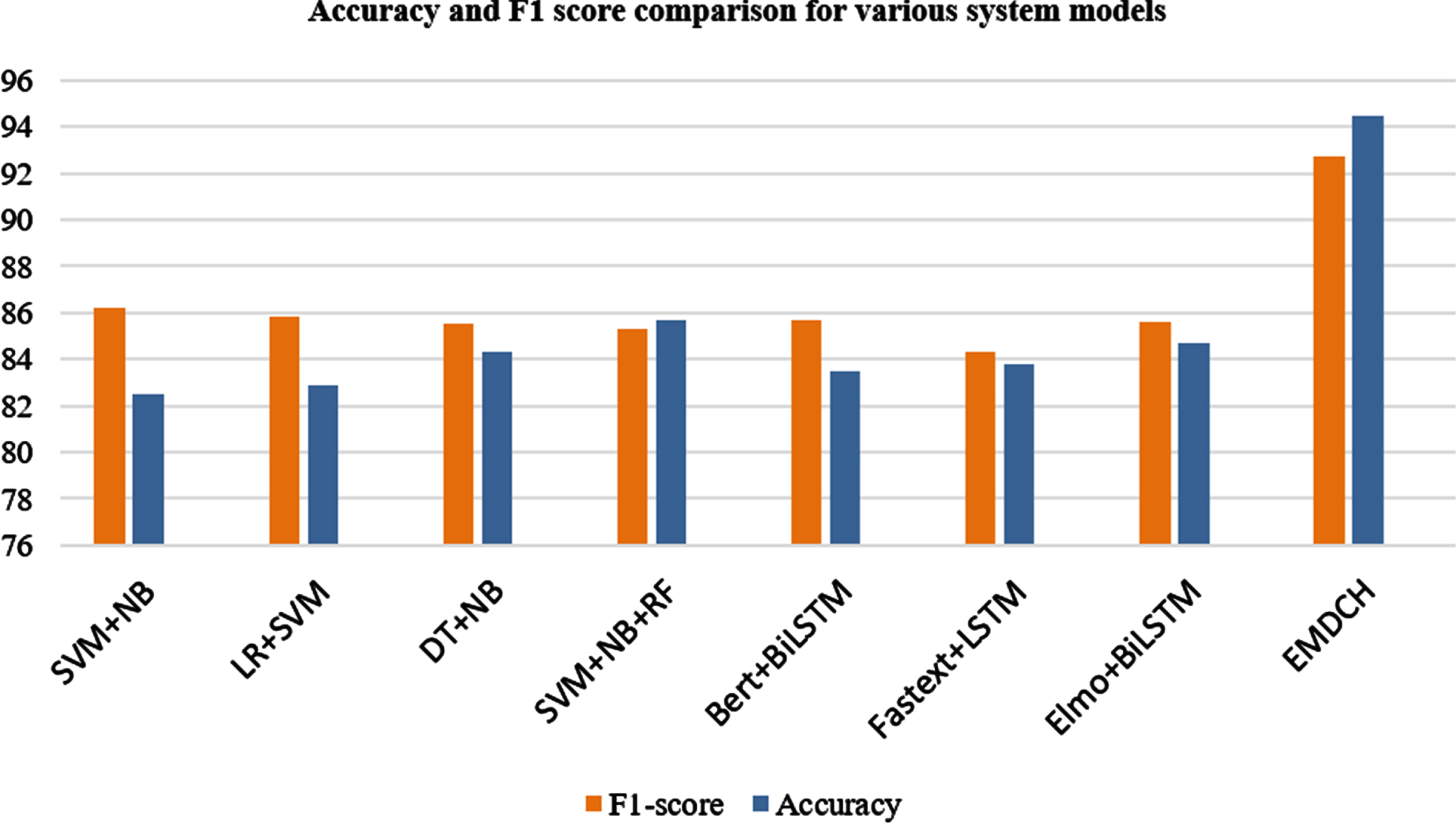
A novel ensemble model for identification and classification of
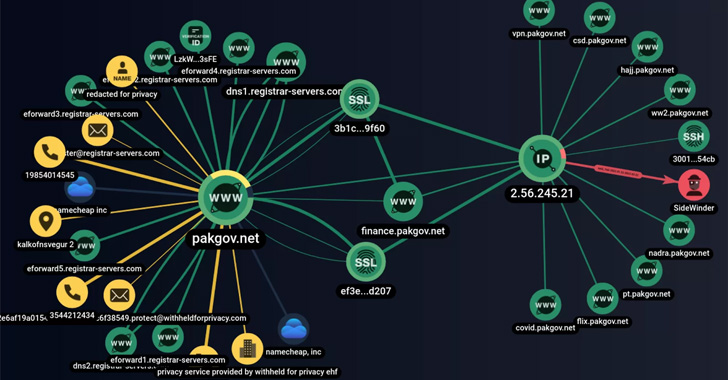
SideWinder Hackers Use Fake Android VPN Apps to Target Pakis
do_more_with_twitter_data/examples/clustering_users/kmeans_bokeh
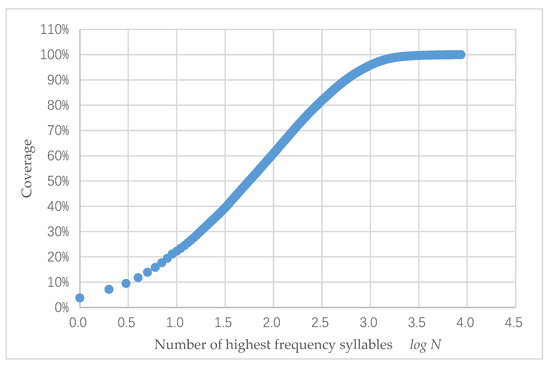
Information, Free Full-Text
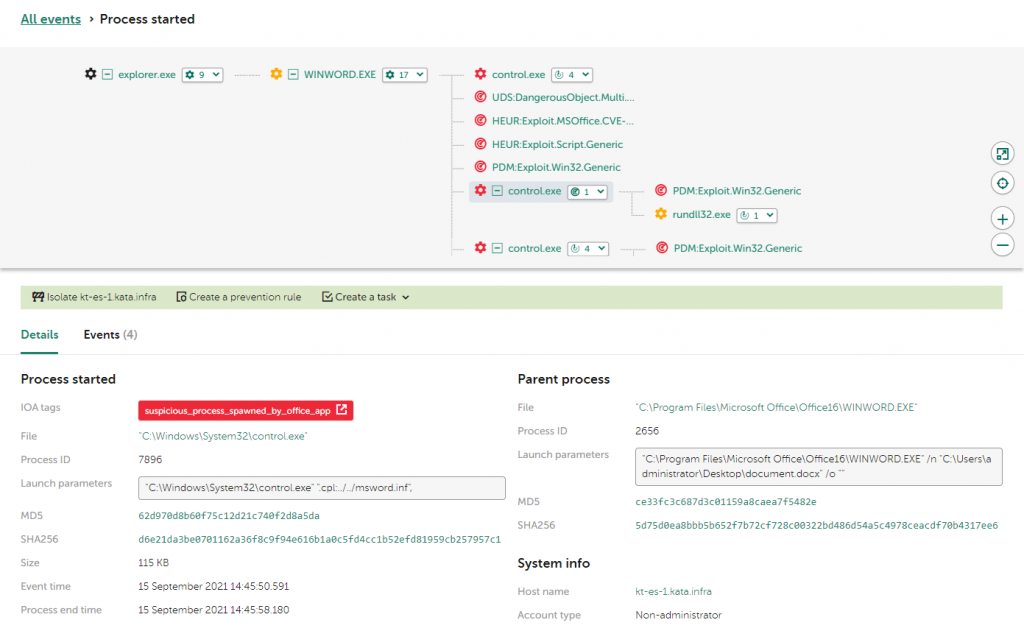
Exploitation of the CVE-2021-40444 vulnerability in MSHTML
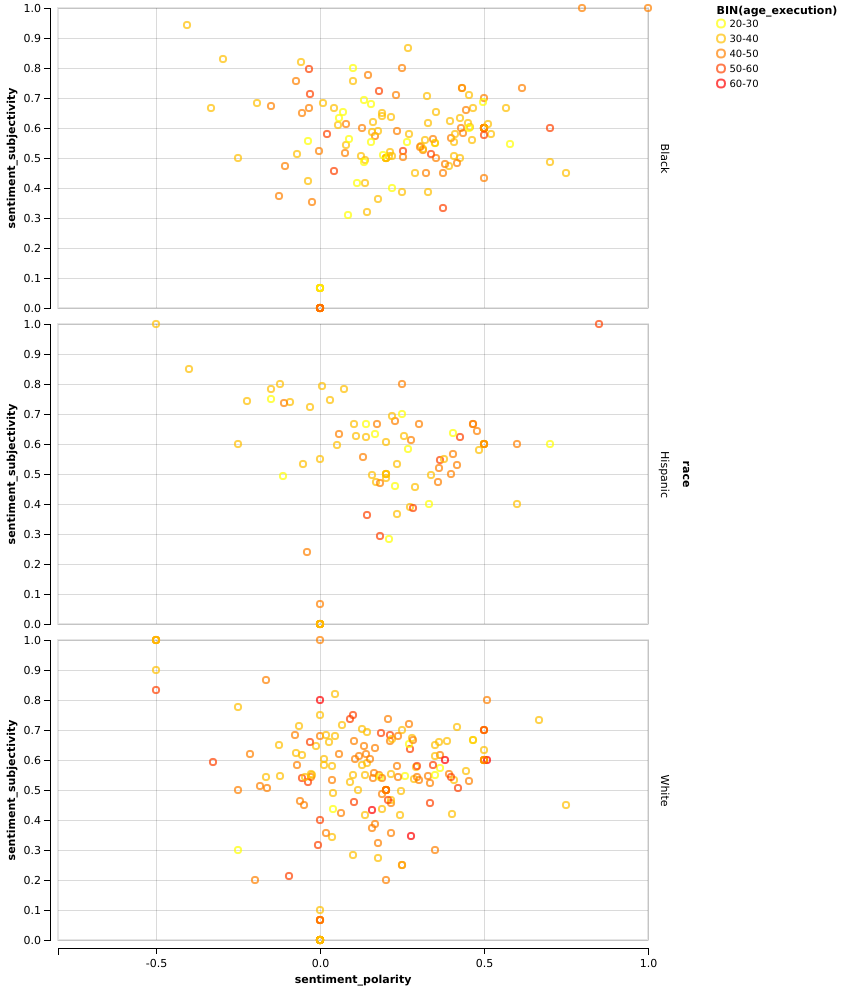
Exploration of Texas death row data

China: Is peak coal part of its problem?
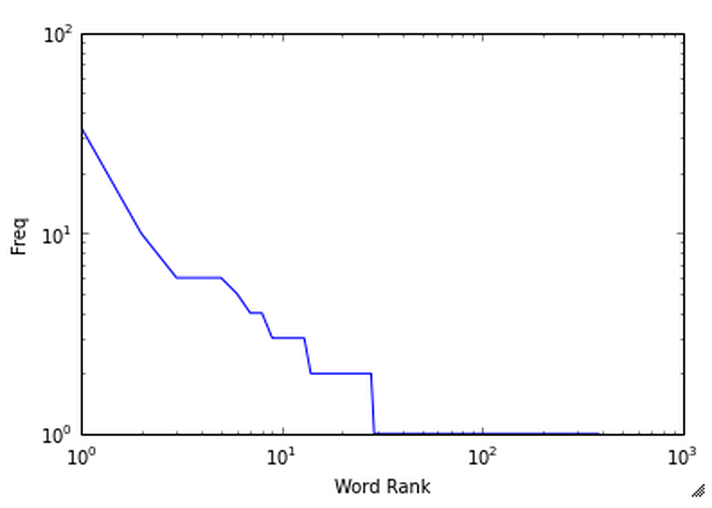
1. Mining Twitter: Exploring Trending Topics, Discovering What
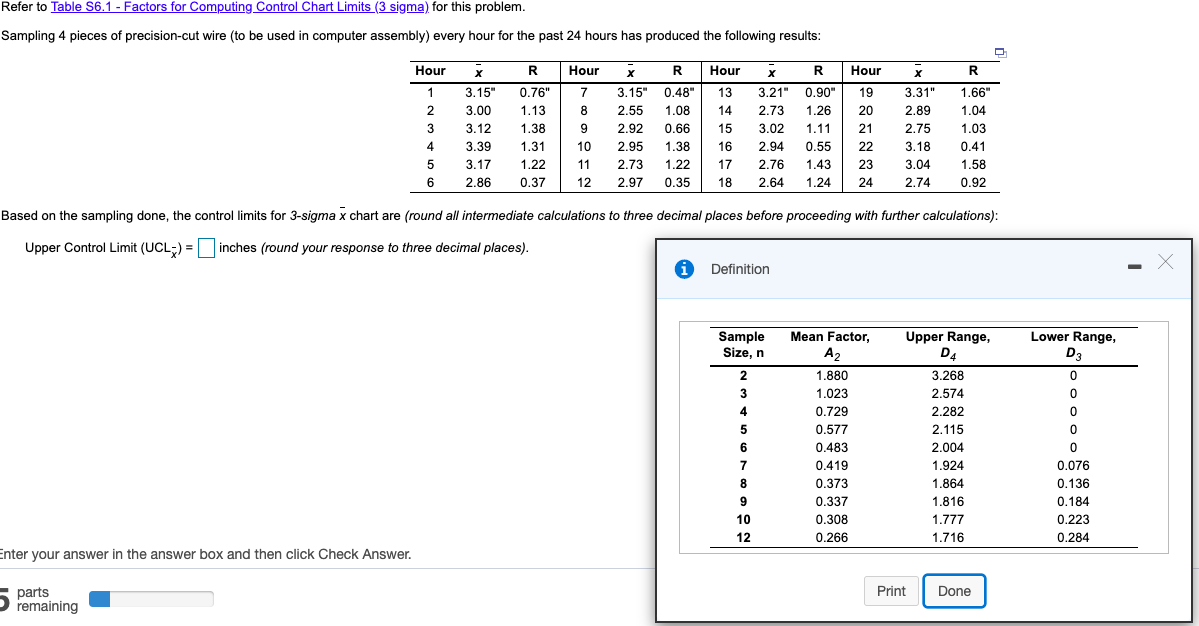
Solved Control limits for 3-sigma x chart are: -Upper
codeparrot/self-instruct-starcoder · Datasets at Hugging Face

Crack Spreads Warn of Future Shortages; Despite Oil Weakness
Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
- Best Price $ 13.00. Good quality and value when compared to dichvuketoan.vn similar items.
- Seller - 632+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

What Is The Best First Designer Bag For You? - PurseBlog
Buy It Now 15d 7h -

Pre-owned LOUIS VUITTON Monogram Cosmetic bag M47522 Brown
Buy It Now 18d 16h -

Louis Vuitton Monogram Bloom Flower Emilie Wallet Purple
Buy It Now 5d 18h -

Louis Vuitton 2006 Pre-owned Danube Crossbody Bag
Buy It Now 27d 16h -

Louis Vuitton x Nike Air Force 1
Buy It Now 4d 22h -

Louis Vuitton Connect on the App Store
Buy It Now 15d 10h -

Louis Vuitton Keepall 45 Bandouliere Damier Graphite Travel Bag Black
Buy It Now 9d 12h -

Louis Vuitton, Bags, Speedy 25 Used But Still In Good Condition
Buy It Now 15d 13h -

Louis Vuitton Opens First U.S. Standalone Men's Store In Miami
Buy It Now 3d 13h -

Vintage Louis Vuitton x Takashi Murakami Monogram Cherry Blossom Poche – Madison Avenue Couture
Buy It Now 7d 7h -

Louis Vuitton Easy Pouch on Strap Black Monogram Empreinte
Buy It Now 28d 19h -

Moclever 5pcs Diaper Bag Tote Set - Baby Bags for Mom (Gray)
Buy It Now 24d 16h -

Louis Vuitton Monogram Canvas Boite Chapeau Souple PM Bag Louis
Buy It Now 11d 17h -

Felpa con cappuccio e glitter - OBSOLETES DO NOT TOUCH 1AAXGK
Buy It Now 16d 15h -

Monogram Comics Intarsia Short-Sleeved Crewneck - Ready to Wear
Buy It Now 27d 12h -

Louis Vuitton Svg - Louis Vuitton Vector - Louis Vuitton Eps
Buy It Now 14d 21h -
Download Louis Vuitton (LV) Logo in SVG Vector or PNG File Format
Buy It Now 8d 21h -

Louis Vuitton Marine Monogram Blocks Tote (SHG-36525)
Buy It Now 28d 7h -

Capucines BB - Luxury Python Natural
Buy It Now 23d 15h -

LV Vitesse T-Shirt Dress - Ready to Wear
Buy It Now 10d 18h -
Replica Louis Vuitton M40458 Kimono Tote Bag Monogram Canvas For Sale
Buy It Now 13d 22h -

Louis Vuitton LV Toiletry 26 Pouch Handbag, Luxury, Bags & Wallets
Buy It Now 2d 10h -

Trying this TikTok trend (branded paper bag DIY into a handbag!)
Buy It Now 21d 5h -

Vuitton Lim.Ed. Mini Backpack Logos - Vintage Lux
Buy It Now 4d 18h
