Authentication
$ 26.50 Buy It Nowor Best Offer, FREE Shipping, 30-Day Returns

The Importance Of Password-based Authentication

9 QUICK TIPS TO IMPROVE WEAK AUTHENTICATION - HALOCK
Authentication: Methods, Protocols, and Strategies
Authentication and Digital Signatures: a 2-in-1 Approach
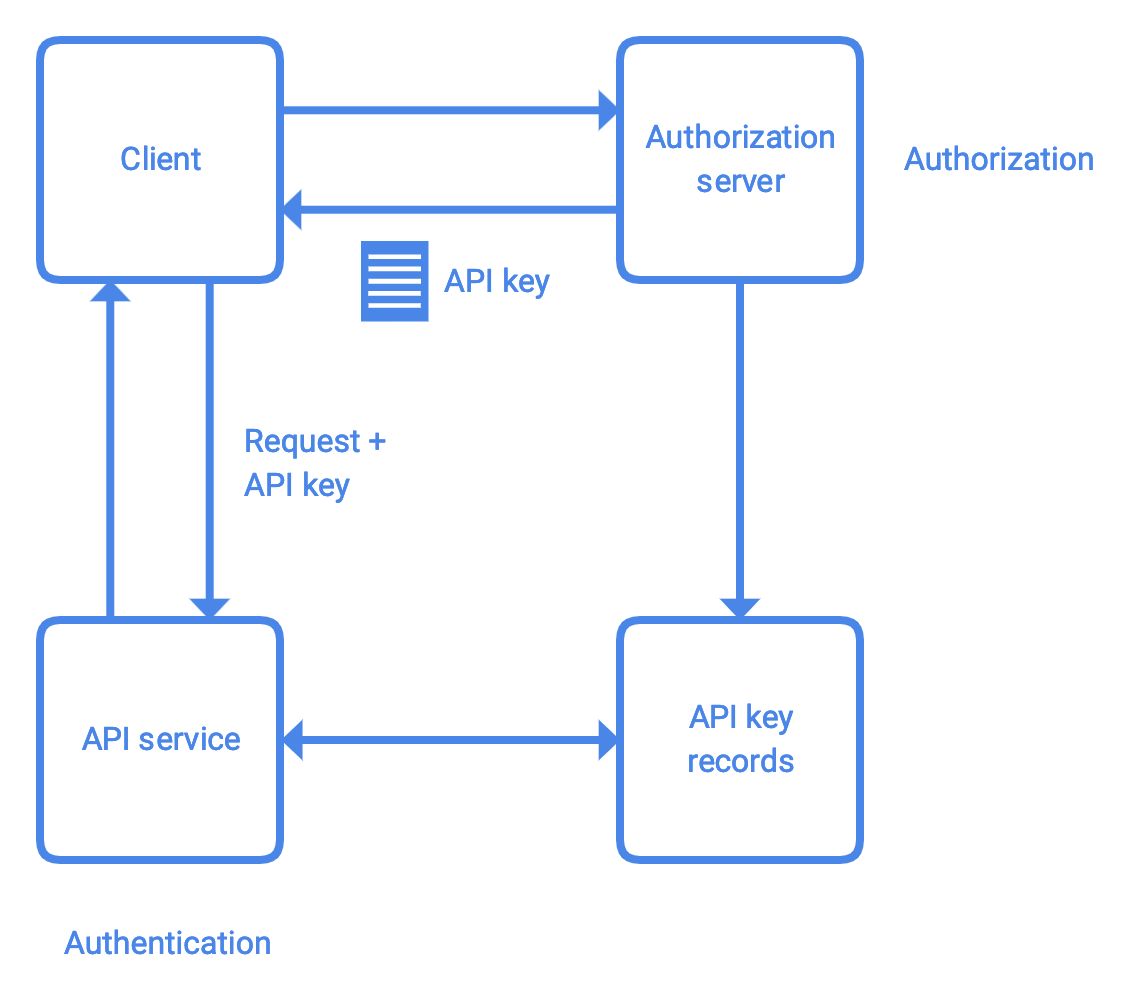
Authorization and Authentication in API services

8 Authentication Methods that Can Secure the Different Industries

Risk-based Authentication

Hey WeLiveSecurity, how does biometric authentication work?

What Is Multi-Factor Authentication (MFA)? How Does it Work?
Authentication
- Best Price $ 26.50. Good quality and value when compared to dichvuketoan.vn similar items.
- Seller - 528+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Capucines BB Capucines - Women - Handbags
Buy It Now 10d 20h -

Louis Vuitton Pallas Chain Monogram Black Shoulder Bag ○ Labellov
Buy It Now 21d 18h -

Charlie Sneaker - Shoes
Buy It Now 10d 16h -

Business Card Holder Damier Azur Canvas - Wallets and Small Leather Goods
Buy It Now 23d 21h -

My Louis Vuitton black bag picks!
Buy It Now 23d 8h -

Louis Vuitton x NBA patch logo T-shirt. Amazing - Depop
Buy It Now 22d 16h -

Louis Vuitton Epi Tribal Mask Pochette Cles (SHG-35513) – LuxeDH
Buy It Now 28d 14h -

Louis Vuitton Monogram Canvas Montaigne MM Bag Louis Vuitton
Buy It Now 8d 7h -

Louis Vuitton Unveils Paradise Accessories Collection
Buy It Now 8d 10h -

Louis Vuitton Monogram Vernis Brea MM Satchel (SHF-20211) – LuxeDH
Buy It Now 23d 18h -
M&M'S Fun Size Milk Chocolate Candy Variety Pack Bulk Candy Bag, 55ct/30.35oz - Kroger
Buy It Now 7d 19h -

Louis Vuitton Moccasin/Loafers/FA 0162 Brown 9.5 EU, 11.5 US
Buy It Now 5d 21h -

With my mini bag. Converse sneakers outfit, Sneakers outfit, Mini bag
Buy It Now 16d 13h -

Bucket Hat with LV Inspired Monogram print made from Faux Fur
Buy It Now 20d 15h -

Louis Vuitton, Bags, Copy Louis Vuitton Eclipse District Mm Messenger Bag
Buy It Now 16d 18h -

Pastel Goth Bag Charm
Buy It Now 18d 11h -
Sneaky Valentine with Skechers — Miss Minus Sized
Buy It Now 15d 5h -

Hilary Duff Hops Into Hair Salon: Photo 2434525
Buy It Now 8d 12h -

Beyoncé Wears Christopher John Rogers Pants & Telfar Bag In
Buy It Now 25d 13h -

Shop New Minions New York Travels Large Schoo – Luggage Factory
Buy It Now 27d 11h -

Adolescent Autumn Winter Plush Sweater Mens Clothing Free Hoodie Boys Clothing American Fashion Print Top Mens Gift - Men's Clothing - Temu Netherlands
Buy It Now 7d 19h -

Auth LOUIS VUITTON Creole Sweet Monogram Hoop Earrings M65679 Silver #W504061
Buy It Now 22d 17h -

Shop Louis Vuitton 2024 SS Monogram Unisex Street Style Leather
Buy It Now 19d 10h -

The Holes Series 3 Books Set by Louis Sachar by Louis Sachar
Buy It Now 23d 5h


